In an astonishing turn of events, Stefan Thomas found himself in possession of a locked USB drive containing a staggering 7,002 bitcoins, valued at approximately $235 million. Unfortunately, Thomas had lost the password to access this digital fortune. The key to unlocking this substantial cryptocurrency cache remained elusive, until one team of hackers embarked on a mission to crack the code.
At 9:30 AM on a Wednesday in late September, a hacker, using the alias “Tom Smith,” reached out with a cryptic text message: “query voltage recurrence.” This message served as tangible evidence of an extraordinary feat—one that held immense potential value. A few days earlier, Thomas had randomly generated this three-word passphrase and set it as the key to access an encrypted USB thumb drive known as an IronKey S200. He had then shipped the USB drive across the country to Unciphered, a startup based in Seattle, for their assistance.
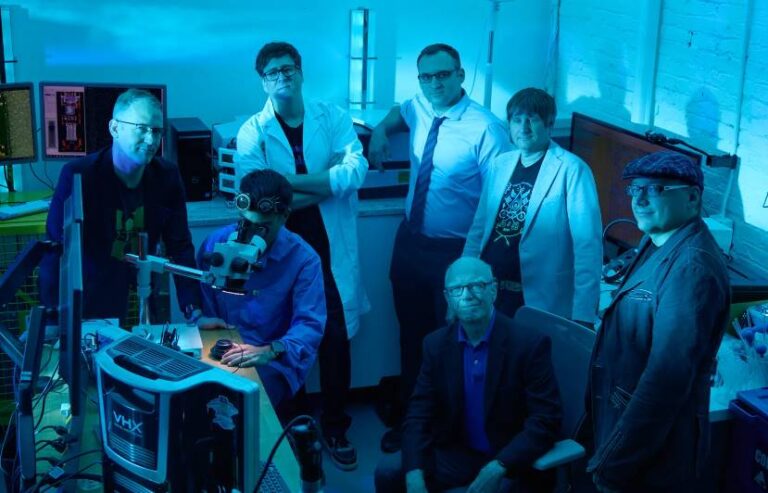
Smith had forewarned Thomas that deciphering this passphrase could take several days, if not longer. In reality, successfully guessing the passphrase should have been a daunting task, as IronKeys are programmed to permanently erase their contents after just 10 incorrect password attempts. Nevertheless, Unciphered’s hackers had devised a covert password-cracking technique, which they have yet to fully disclose to the public. This technique effectively provided them with an infinite number of attempts to guess the passphrase. Remarkably, my USB drive had reached Unciphered’s lab on Tuesday, and within a remarkably short span of time, I received my three-word passphrase via text message on the following morning.
Smith explained that, with the assistance of a high-performance computer, the process of cracking the code had required a staggering 200 trillion attempts. The remarkable story of Thomas’ lost bitcoin fortune and the unconventional efforts undertaken to regain access to it continues to unfold, leaving observers captivated and perplexed in equal measure